Zones
Network segmentation into security zones is a measure to minimize the impact when one zone is compromised. The security level of one zone can be different from another zone. In case zones shall be introduced either at the initial project design or as a later extension is not the topic of this document, however the example is meant to clarify the concept and highlight possible options.
Possible zones in a typical NMS implementation are:
• The Management Control Network (MCN);
• The regions of the MCN, if there is regional partitioning;
• The NMS Interconnection Network (NIN);
• The internal company network;
• The Internet.
Note that not all zones are always present. In the case of an NMS consisting of a single server, exclusively connected to the MCN, there is only the MCN zone. In this case, protection might be limited to physical access protection and the use of proper passwords.
Added standby servers (see [1KHW029097] User Manual – FOXMAN-UN Main/Standby Solution) and/or client computers are often interconnected using a separate IP network. This NMS Interconnection Network (NIN) creates a second security zone, which blocks direct access to the MCN from the client computers. Clients can only access the MCN through the NMS applications. As the NMS server does not route traffic between MCN and NIN no direct access to the MCN is possible. Other zones may be assigned within the MCN itself. Regional responsibilities in a large network can be one reason; the use of third party communication services another. Regional responsibilities may require the addition of external router and the use of IP address based access control lists. This is to allow the central NMS servers to access all network devices the regional network Devices are however not able to connect to devices in other regions. To facilitate such configuration, it is good practice to assign distinct IP address ranges to each region from the very beginning of a project.
The use of third party communication services may prompt the use of encryption on the corresponding network connection.
More critical security issues may arise from an NMS that is directly connected to the internal company network in turn connected to the Internet. The use of firewalls is a strong requirement in this case. In addition, IP based access control lists and role based access control should be used.
The picture below highlights the discussed zones in different colors.
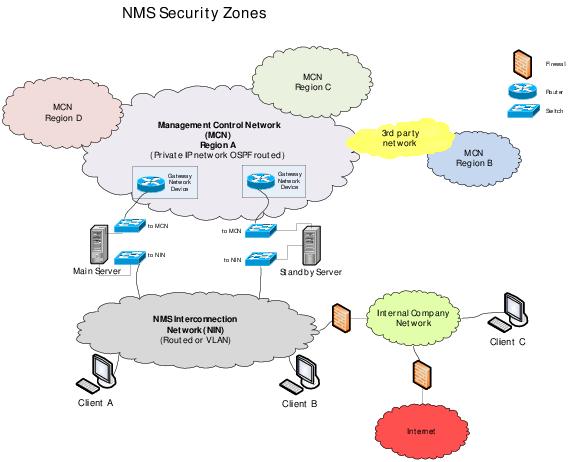
NMS Security Zones
